[OpenClaw] Is OpenClaw Secure Enough for Customer Data? What Enterprises Need to Know
A security analysis of OpenClaw for enterprise use. Understand the risks of using open-source AI agents with customer data and what security controls are needed.
![[OpenClaw] Is OpenClaw Secure Enough for Customer Data? What Enterprises Need to Know](/content/images/size/w1200/2026/02/Anyreach-Openclaw-Blog-Cover--4--3.png)
A Security Architecture Designed for One
OpenClaw's security model is straightforward: the agent is as secure as the machine it runs on, and it has access to everything the host machine can reach. This is a perfectly reasonable design for a personal AI assistant running on your own hardware for your own tasks.
But this model fundamentally breaks down when applied to customer data. Customer data carries legal obligations, regulatory requirements, and trust expectations that demand purpose-built security infrastructure. The question is not whether OpenClaw is a well-built project — it is — but whether its architectural foundations can support the security requirements that customer data handling demands.

What Enterprise Security Requires
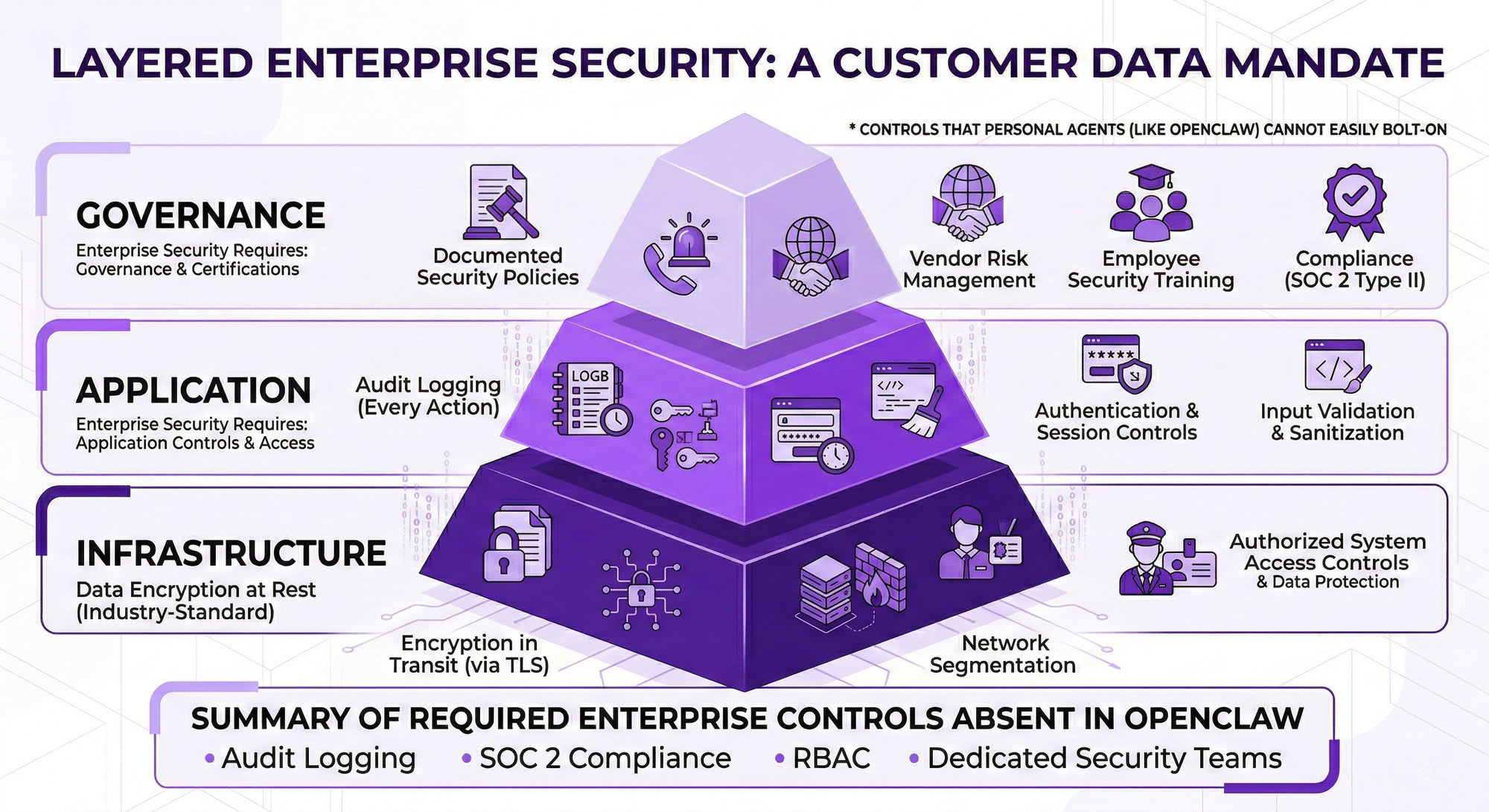
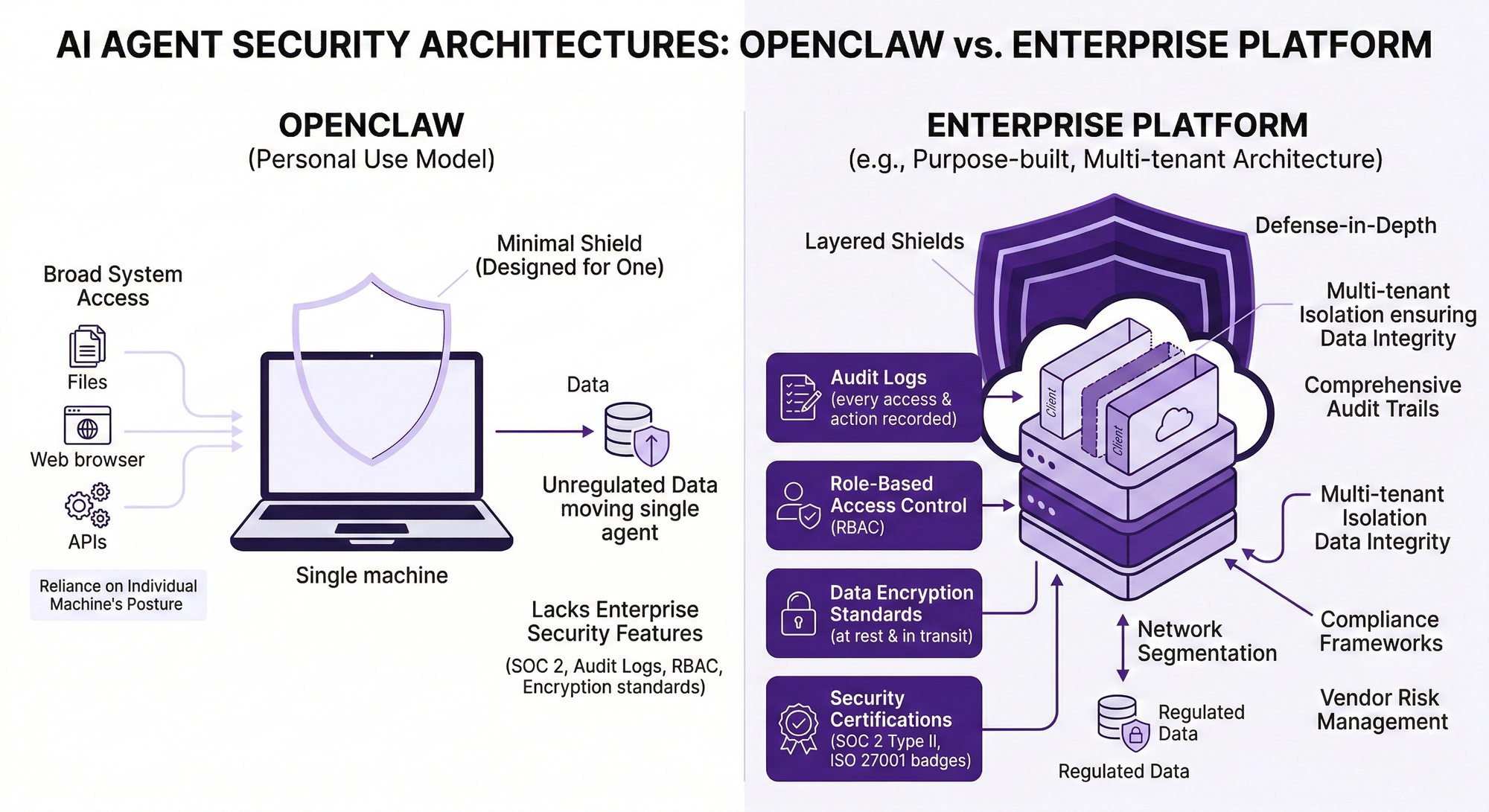
Handling customer data in an enterprise context requires a layered security approach that OpenClaw's architecture does not provide. At the infrastructure level, enterprises need data encryption at rest using industry-standard algorithms, encryption in transit via TLS, network segmentation isolating data processing environments, and access controls that limit data exposure to authorized systems and personnel.
At the application level, enterprises need audit logging that records every data access and action, role-based access controls that enforce least-privilege principles, session management and authentication controls, input validation and output sanitization, and regular security assessments including penetration testing.
At the governance level, enterprises need documented security policies, incident response procedures, vendor risk management, employee security training, and compliance certifications like SOC 2 Type II that provide independent verification of security controls.
OpenClaw provides none of these capabilities as part of its core platform. The community may develop security-oriented skills and configurations, but bolt-on security for a platform that was not designed with these constraints is fundamentally different from security-by-design.
The CrowdStrike Warning and Industry Concerns
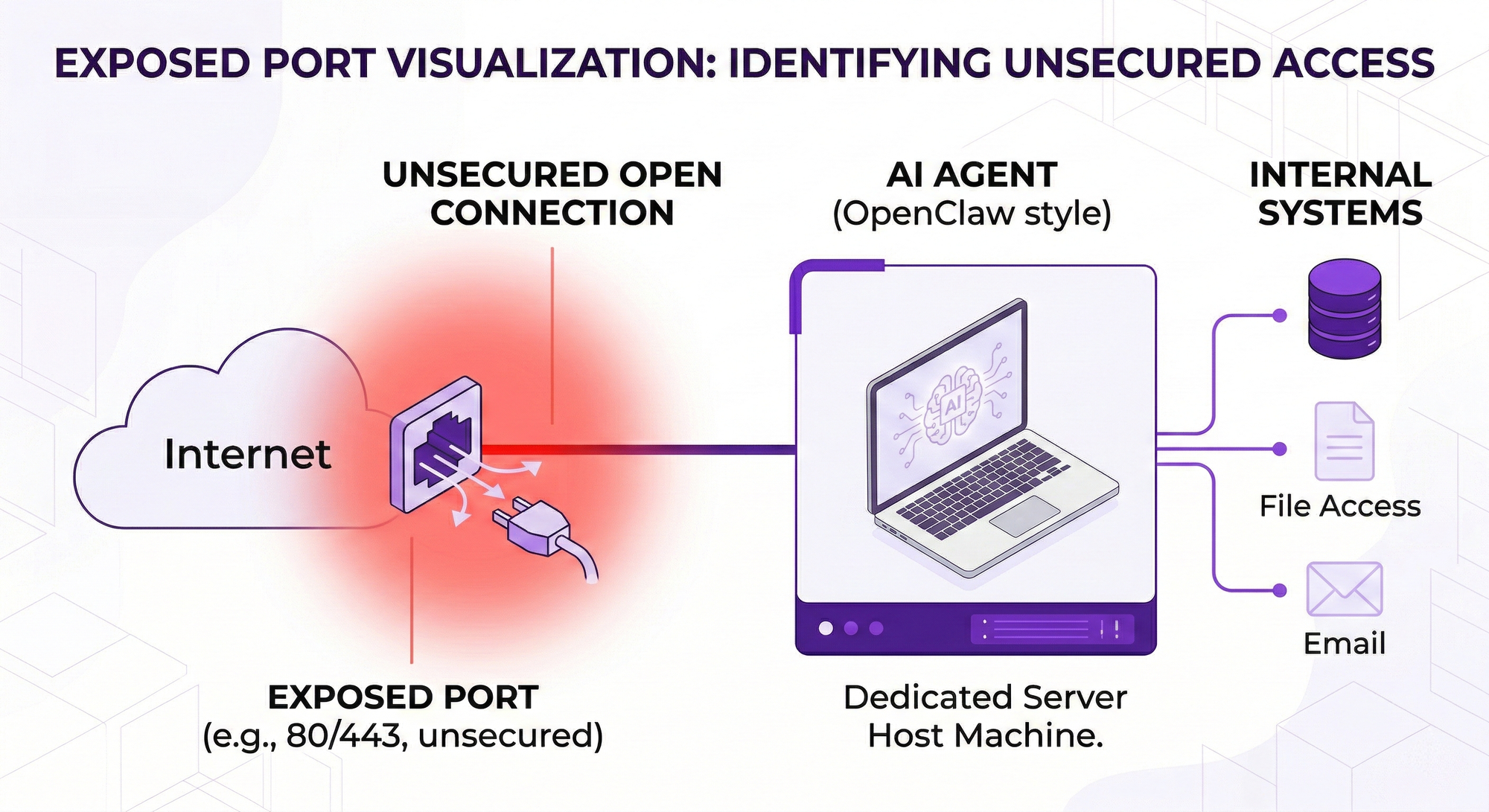
Security researchers and organizations have already raised alarms about the risks inherent in platforms like OpenClaw. CrowdStrike and others have noted that giving an AI agent broad system access — the ability to read files, execute commands, browse the web, and interact with APIs — creates a powerful attack surface.
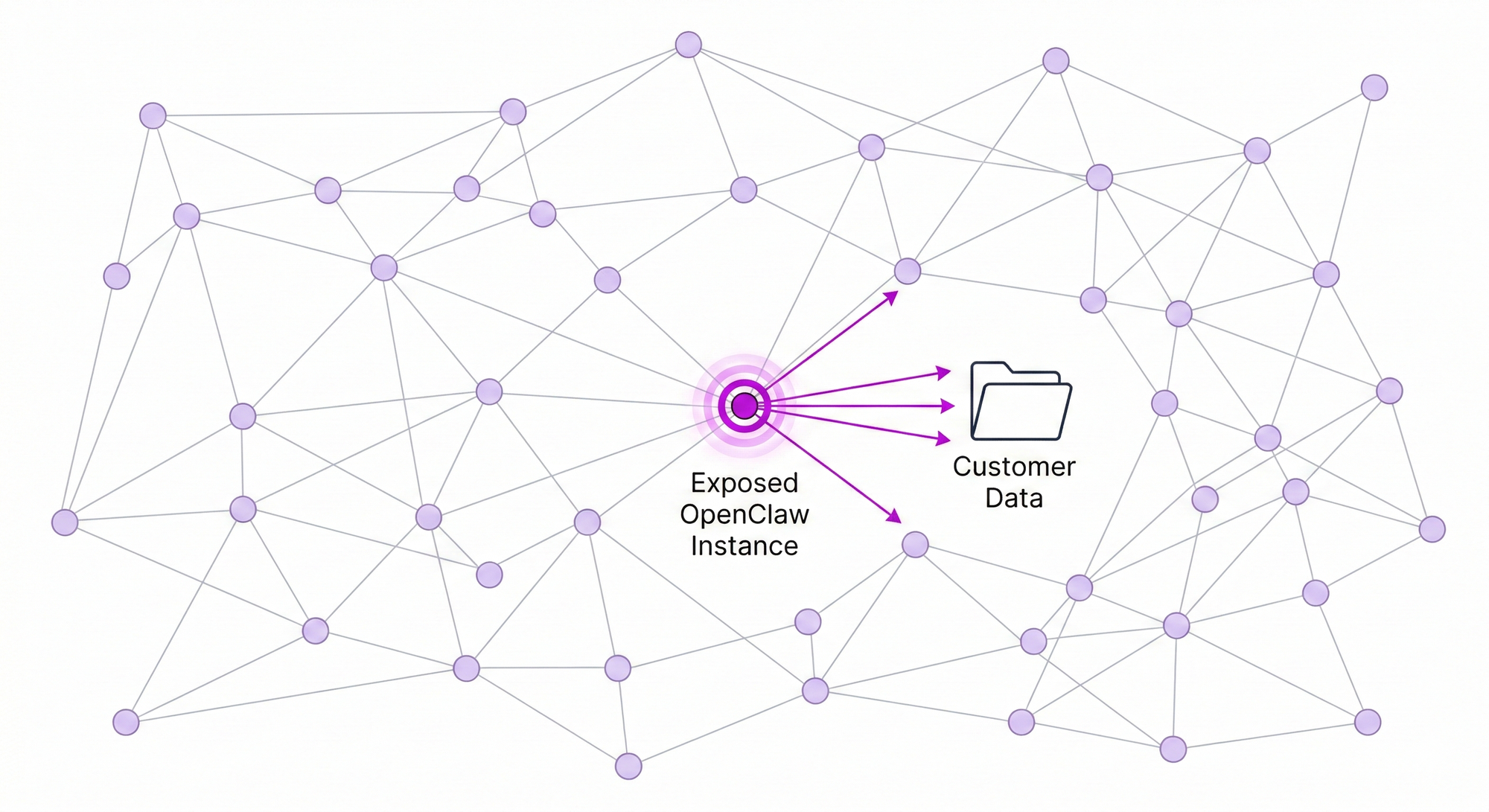
Exposed OpenClaw instances have already been discovered on the public internet. Each exposed instance potentially gives an attacker access to everything the agent can reach, including connected email accounts, messaging platforms, file systems, and any API the agent has credentials for.
For organizations considering using OpenClaw with customer data, this risk profile should be disqualifying. A single misconfiguration, a single exposed port, a single compromised credential could result in unauthorized access to customer information at a scale determined by whatever data the agent has been connected to.
What Customer Data Handling Actually Requires
Organizations that handle customer data responsibly deploy purpose-built infrastructure with security as a foundational requirement. Enterprise AI agent platforms like Anyreach are architected from the ground up with these constraints in mind.
This means multi-tenant data isolation ensuring one customer's data never bleeds into another's operations. It means comprehensive audit trails that demonstrate exactly what data was accessed, when, by which agent, and what actions were taken. It means compliance certifications that have been independently verified by third-party auditors. It means incident response capabilities, vulnerability management programs, and security teams dedicated to maintaining the platform's security posture.
The gap between OpenClaw's personal-use security model and what customer data handling requires is not a gap that can be bridged with configuration changes or community plugins. It requires a fundamentally different architectural approach.
Frequently Asked Questions
Is OpenClaw safe to use with customer data?
OpenClaw was designed as a personal AI agent and lacks the enterprise security controls required for customer data handling, including SOC 2 compliance, audit logging, role-based access control, and data encryption standards. Security researchers have flagged exposed instances and architectural risks.
What security certifications does OpenClaw have?
OpenClaw does not have enterprise security certifications such as SOC 2, ISO 27001, or HIPAA compliance. As an open-source project designed for personal use, these certifications are not part of its scope.
What is the safest way to deploy AI agents for customer interactions?
The safest approach is using a purpose-built enterprise AI agent platform with security certifications, audit logging, data encryption, role-based access controls, and compliance frameworks designed for customer data handling from the ground up.
Ready for Enterprise-Grade AI Agents?
Anyreach delivers the agentic AI capabilities your organization needs with the security, compliance, and scalability enterprise operations demand. See how Anyreach can transform your customer and employee experience with AI agents that actually do things.


![[BPO Insights] Why Every AI Voice Deployment We Close Ends Up in Healthcare: The Accidental Beachhead](/content/images/size/w600/2026/02/04_the_builders_log-10.png)
![[BPO Insights] The AI Pricing Divide: How Platform Fee Structures Impact BPO AI Adoption Across Market Segments](/content/images/size/w600/2026/02/03_the_uncomfortable_math-10.png)
![[OpenClaw] Your Employees Are Already Using OpenClaw for Work — Here's Why That Should Worry You](/content/images/size/w600/2026/02/Anyreach-Openclaw-Blog-Cover--4--2.png)
![[BPO Insights] The AI Trainer Reframe: How One Narrative Shift Turned Agent Replacement Fear Into a $35/Hour Billing Rate](/content/images/size/w600/2026/02/02_from_the_other_side-10.png)