[OpenClaw] OpenClaw for Business: Why IT and Security Teams Are Saying No
IT and security teams are blocking OpenClaw for business use. Understand the specific concerns and what enterprises should deploy instead for AI agent capabilities.
![[OpenClaw] OpenClaw for Business: Why IT and Security Teams Are Saying No](https://storage.ghost.io/c/40/ac/40ac18d7-d0cb-4132-9e8b-e6740dedd4ad/content/images/size/w1200/2026/02/Anyreach-Openclaw-Blog-Cover--4--11.png)

The Pattern Playing Out in Enterprises Everywhere
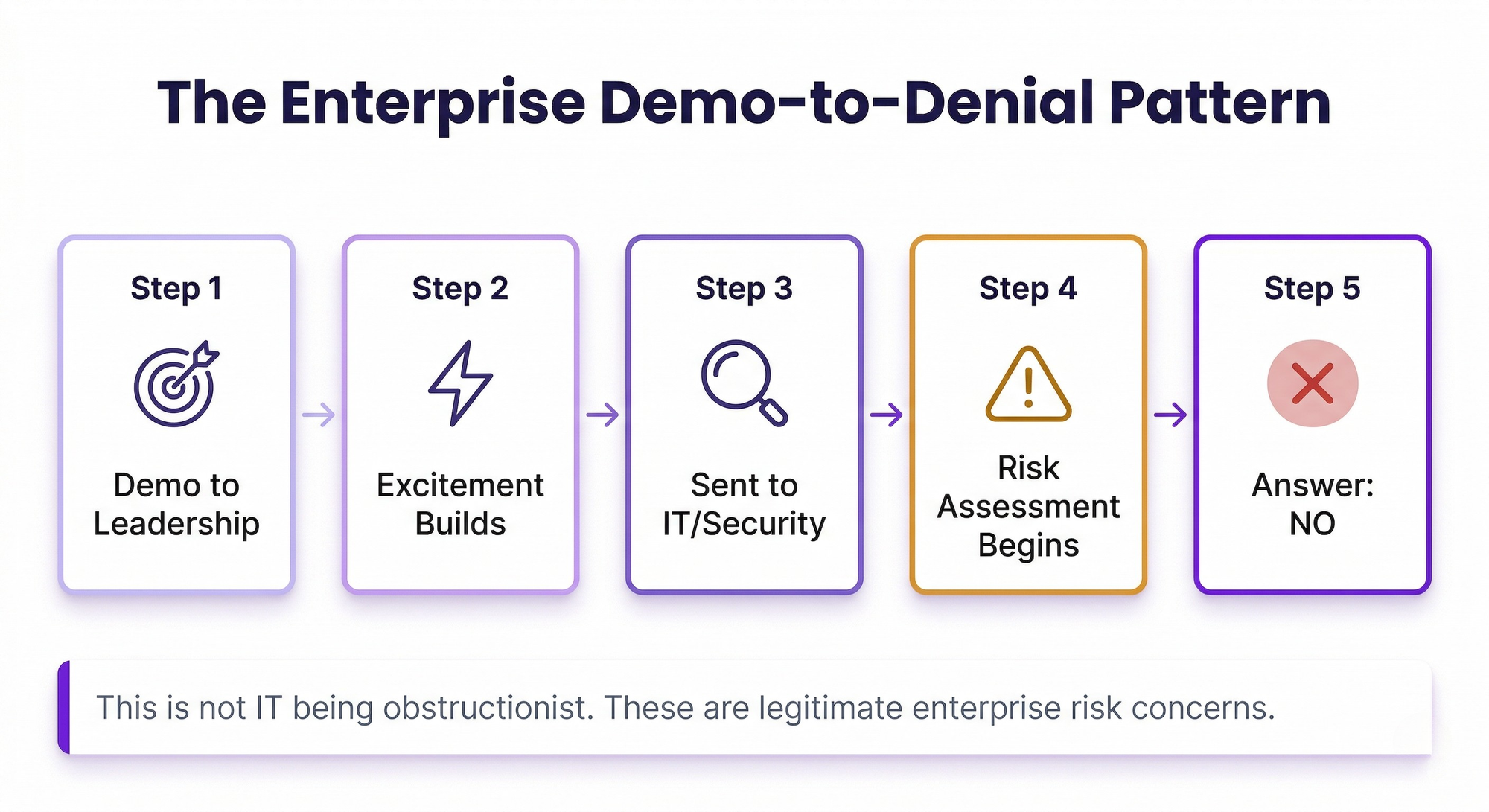
The scenario is becoming increasingly common. A business unit leader, a team lead, or an enthusiastic engineer demonstrates OpenClaw to leadership. The demo is impressive — an AI agent that actually sends emails, manages tasks, and automates real work. Excitement builds. Then the request goes to IT and security for evaluation. And the answer comes back: no.
This is not IT being obstructionist. When security professionals evaluate OpenClaw through the lens of enterprise risk management, they identify legitimate concerns that are difficult or impossible to mitigate within the platform's current architecture.
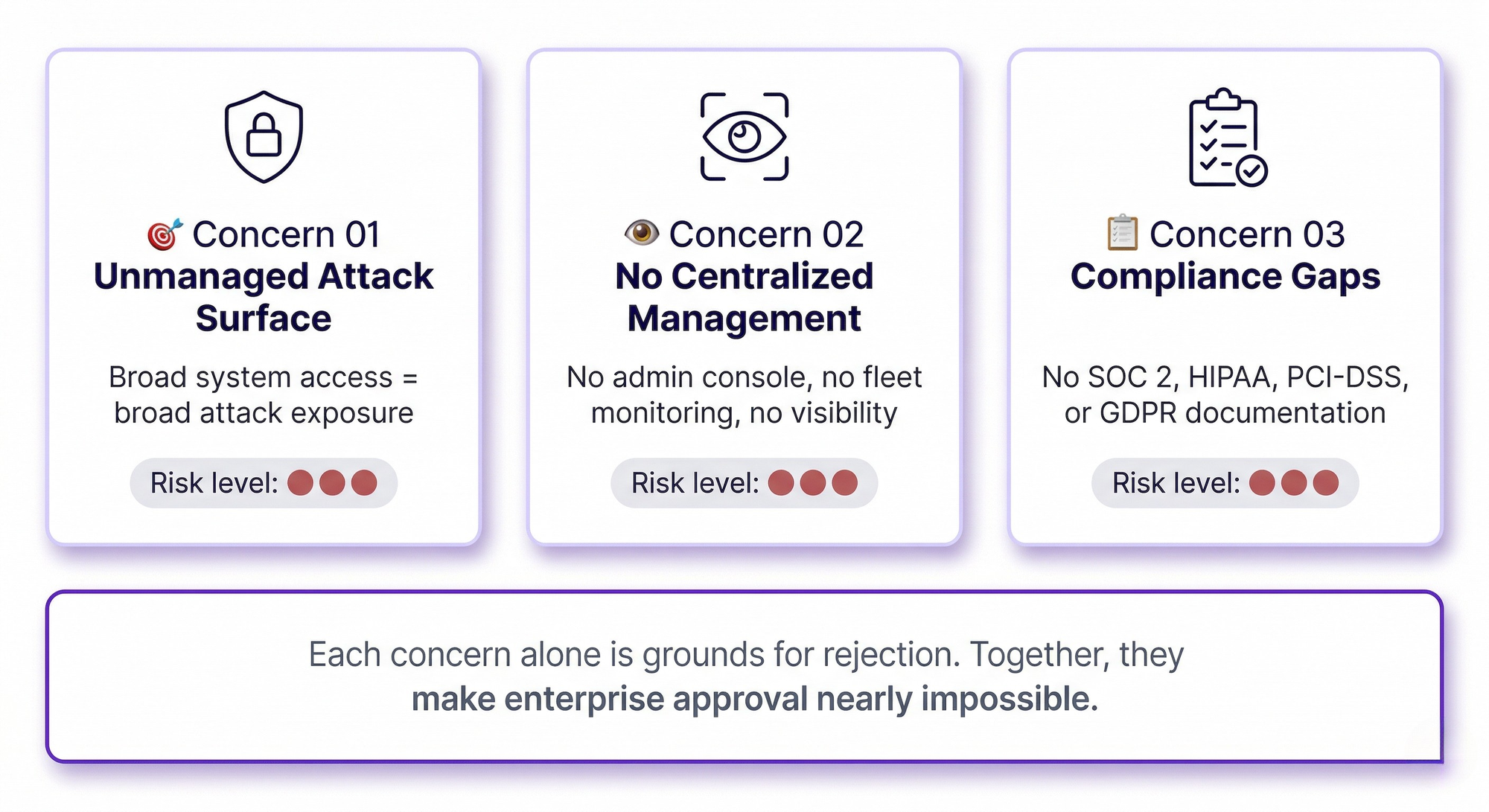
Concern One: Unmanaged Attack Surface
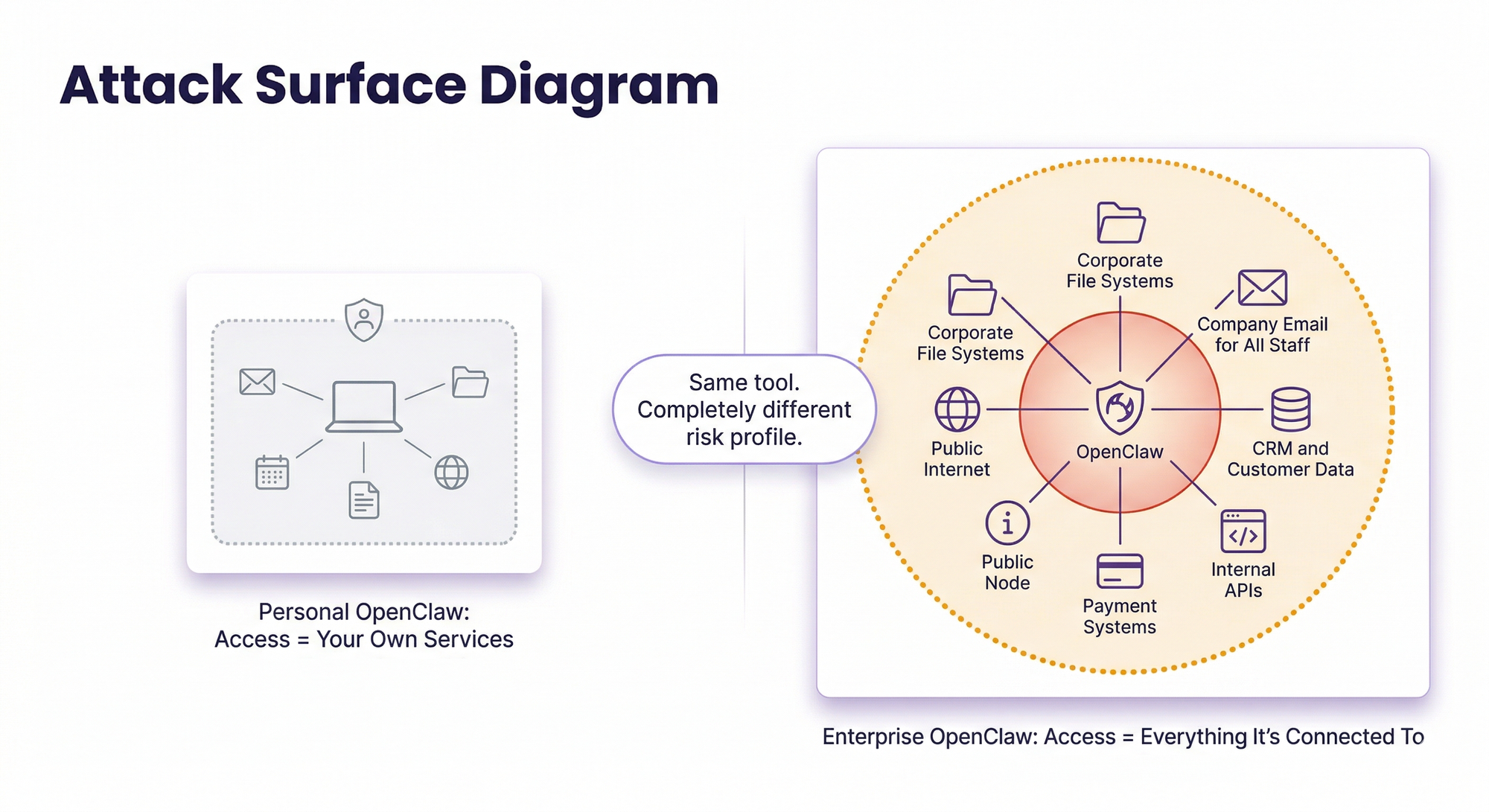
OpenClaw is designed to have broad system access — that is precisely what makes it powerful. It can read files, execute commands, browse the web, send messages, and interact with APIs. For a personal tool on a personal machine, this access model is acceptable because you are granting access to yourself.
In an enterprise context, this access model is a security team's concern. Each OpenClaw instance creates a powerful node on the network that can reach whatever systems it has been connected to. If the instance is compromised — through a vulnerable skill, a misconfiguration, or a supply chain attack on the open-source codebase — the attacker inherits all of that access.
Security teams are responsible for maintaining a defensible perimeter and minimizing attack surface. Approving a platform whose core design philosophy is maximum access runs directly counter to that responsibility.
Concern Two: No Centralized Management
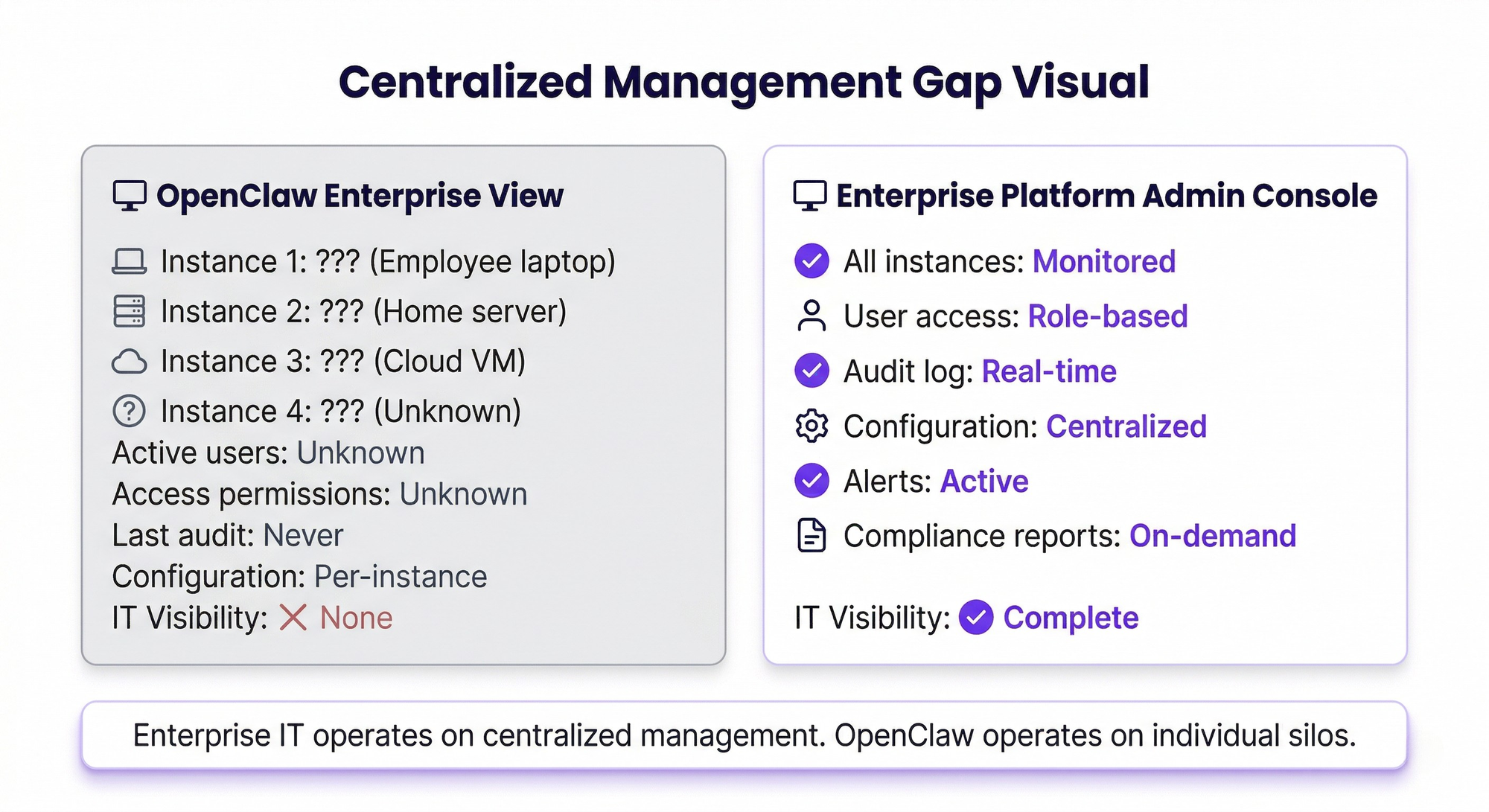
Enterprise IT operates on the principle of centralized management and monitoring. Every approved tool has dashboards, alerting, access management, and audit capabilities that give IT visibility into its operation.
OpenClaw instances are individually managed. There is no enterprise admin console, no centralized access management, no fleet-wide monitoring, and no standardized configuration management. Each instance is its own silo, configured by whoever set it up, with whatever access they decided to grant.
For IT teams responsible for maintaining visibility across the technology landscape, this lack of centralization is disqualifying.
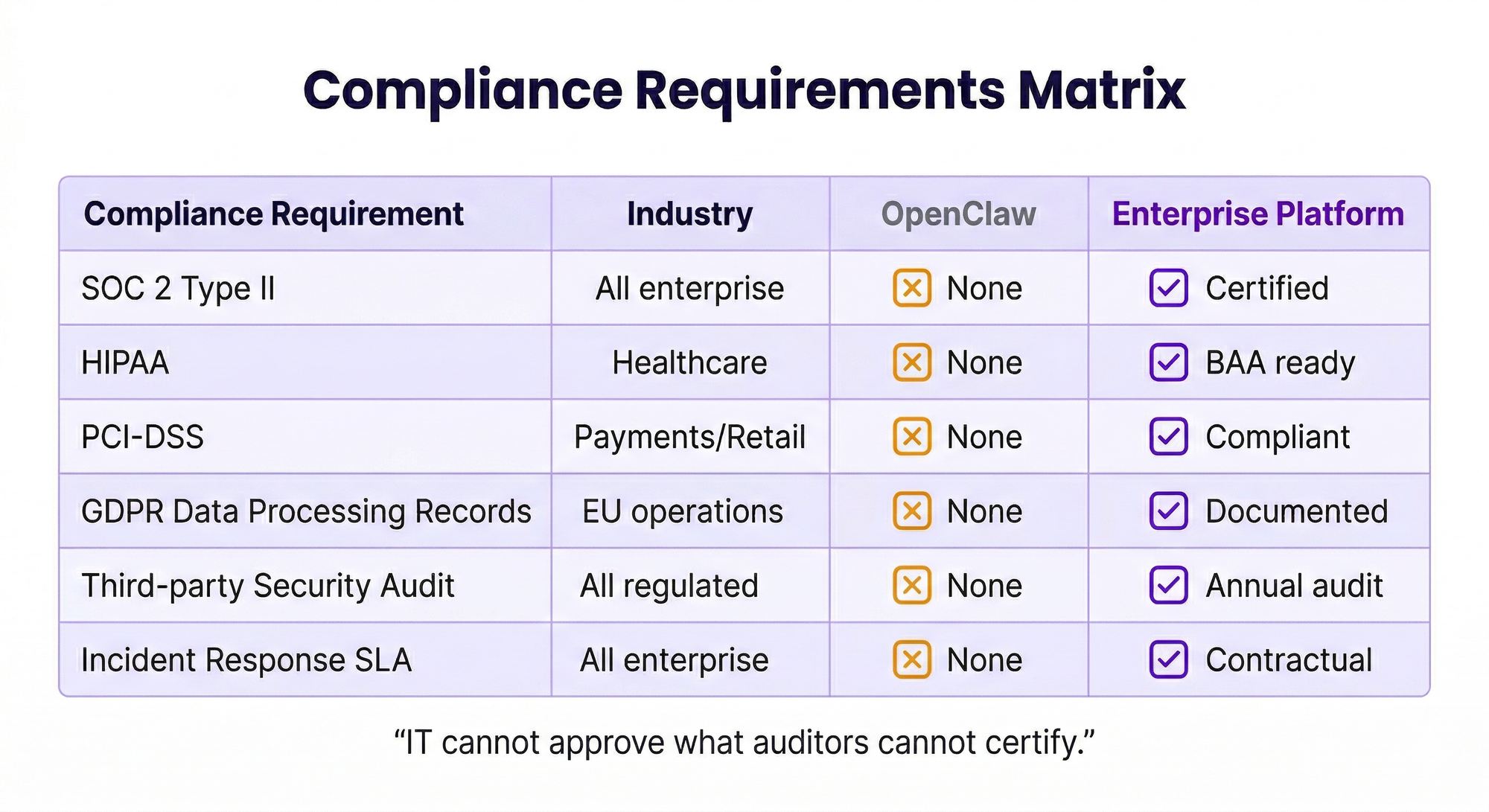
Concern Three: Compliance Requirements
Organizations in regulated industries need every system handling sensitive data to meet specific compliance requirements. OpenClaw does not provide SOC 2 compliance documentation, HIPAA-compliant architecture for healthcare data, PCI-DSS controls for payment data, GDPR data processing records for European data, or any third-party security audit reports.
IT and security teams cannot approve a platform for business use that would create compliance gaps. The risk of regulatory findings, fines, and reputational damage from non-compliant data handling outweighs any productivity gains the tool provides.
What IT Teams Should Recommend Instead
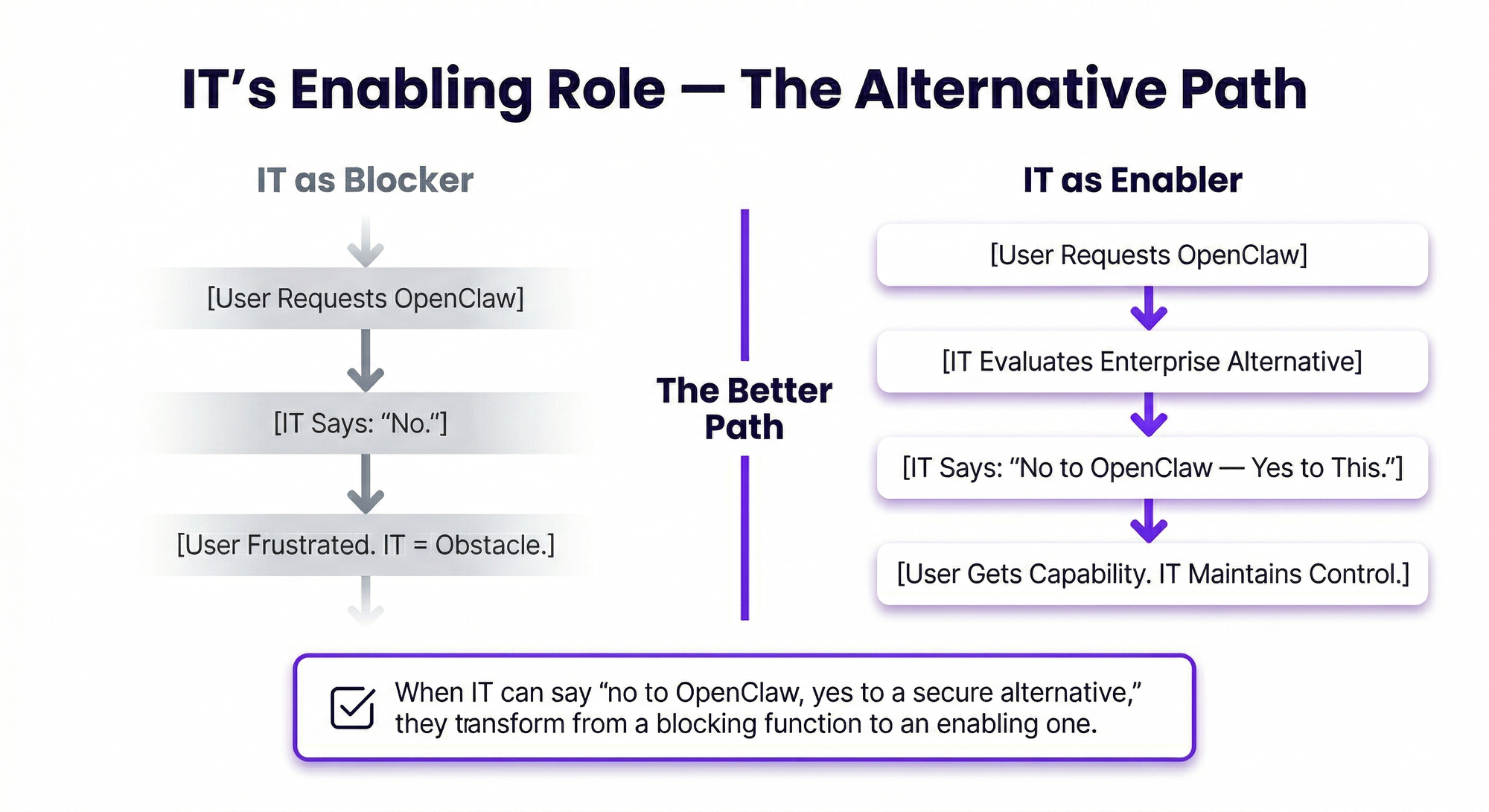
The best IT leaders recognize that the demand behind OpenClaw adoption requests is legitimate. Users want AI agents that take real action. Rather than simply saying no, forward-thinking IT organizations evaluate enterprise AI agent platforms that deliver the same capabilities within an approvable security and compliance framework.
Enterprise platforms like Anyreach provide centralized management and monitoring, role-based access controls, compliance certifications, encrypted data handling, comprehensive audit logging, professional support with SLAs, and managed infrastructure that IT can integrate into existing monitoring and security tooling.
When IT can say 'no to OpenClaw, yes to a secure alternative,' they transform from a blocking function to an enabling one — and the organization captures the productivity benefits that users are seeking.
Frequently Asked Questions
Why do IT teams block OpenClaw for business use?
IT and security teams block OpenClaw due to its unmanaged attack surface, lack of centralized management, absence of enterprise security certifications, compliance gaps, and inability to enforce organizational access controls and data governance policies.
Can OpenClaw be made enterprise-ready?
While possible to harden OpenClaw for enterprise use, it requires significant custom engineering for security, compliance, and management capabilities that are not part of the core platform. Most organizations find it more practical to adopt purpose-built enterprise AI agent platforms.
What should IT recommend instead of OpenClaw?
IT teams should evaluate enterprise AI agent platforms with SOC 2 compliance, centralized management, role-based access controls, audit logging, and professional support that deliver similar AI agent capabilities within an approvable governance framework.
Ready for Enterprise-Grade AI Agents?
Anyreach delivers the agentic AI capabilities your organization needs with the security, compliance, and scalability enterprise operations demand. See how Anyreach can transform your customer and employee experience with AI agents that actually do things.


![[BPO Insights] The Hardest Conversation I Have Every Week: Telling BPO Operators Their Timeline Is Wrong](https://storage.ghost.io/c/40/ac/40ac18d7-d0cb-4132-9e8b-e6740dedd4ad/content/images/size/w600/2026/02/04_the_builders_log-23.png)
![[BPO Insights] 200 Missed Weekend Calls: The Real Cost of No After-Hours Coverage, Quantified Down to the Dollar](https://storage.ghost.io/c/40/ac/40ac18d7-d0cb-4132-9e8b-e6740dedd4ad/content/images/size/w600/2026/02/03_the_uncomfortable_math-23.png)
![[BPO Insights] "Your AI Needs to Navigate EPIC Without an API" — The Desktop Agent Moment That Changes Everything for Healthcare BPOs](https://storage.ghost.io/c/40/ac/40ac18d7-d0cb-4132-9e8b-e6740dedd4ad/content/images/size/w600/2026/02/02_from_the_other_side-23.png)
![[BPO Insights] The RFP Is Changing: What Enterprise Buyers Now Require That They Didn't 18 Months Ago](https://storage.ghost.io/c/40/ac/40ac18d7-d0cb-4132-9e8b-e6740dedd4ad/content/images/size/w600/2026/02/01_cx_intelligence_drop-24.png)